Quantum computing, encryption and cyber security
Basic concepts, myth-busters and practical guidance
The basics about quantum computing, encryption and cyber security
As well as providing new opportunities, quantum computers can create new risks. One commonly discussed is the cyber security threat, in particular to encryption. But what really is the threat, and what should we be doing?
Part 2: Busting myths about the quantum risks to encryption and cybersecurity
The impact of quantum computing on encryption is is plagued with misunderstandings and misconceptions. So, to help organisations make the right decisions, it’s time to bust some of the most common myths.
Myth 1: all encryption is at risk
Part 3: Busting myths about solutions for the quantum threats to encryption
There is also confusion about the solutions for the challenges to encryption, creating myths that can lead to poor decisions. Hopefully this will help you to identify which sources you can trust, and which ones are selling snake oil.
Myth 1 – Quantum random number generators will make you quantum safe
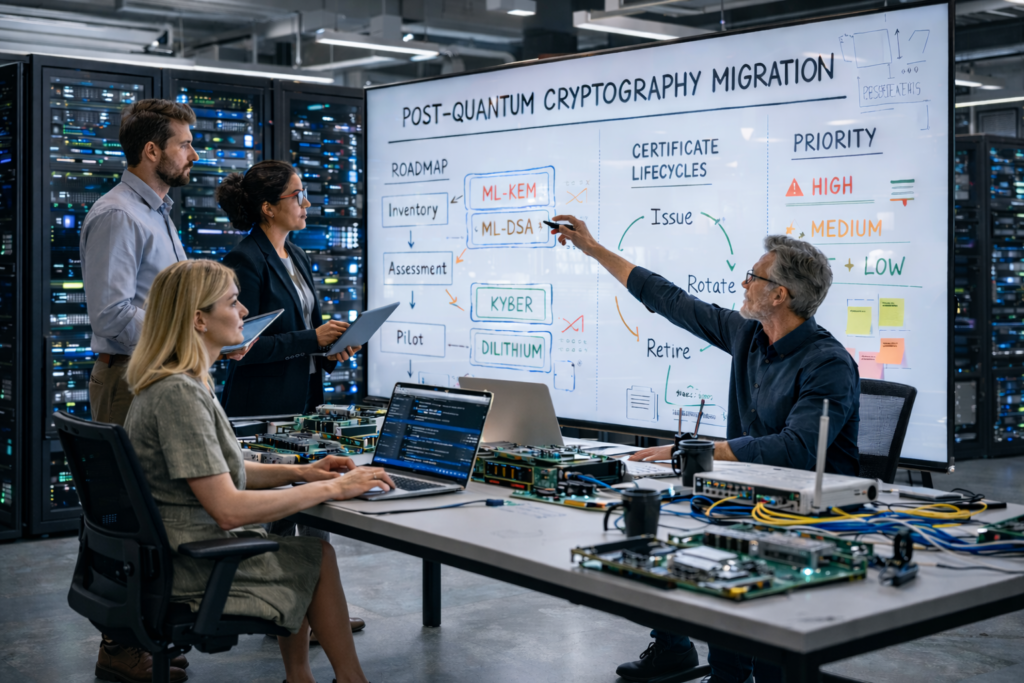
Part 4 – A practical guide to start planning your transition to post-quantum cryptography
Although a “cryptographically relevant quantum computer” may be several years away, you really should start now to understand and plan what you need to do to be ready.
This article reviews some of the potential challenges to getting started, and then walk through some simple suggestions to help you to understand, prioritise and…
Part 5 – Implementing Quantum-Resistant Encryption
This article moves on to look at executing on your plan – in particular how to choose the appropriate solutions, to implement them effectively, and to future-proof your systems so that they are sustainable.