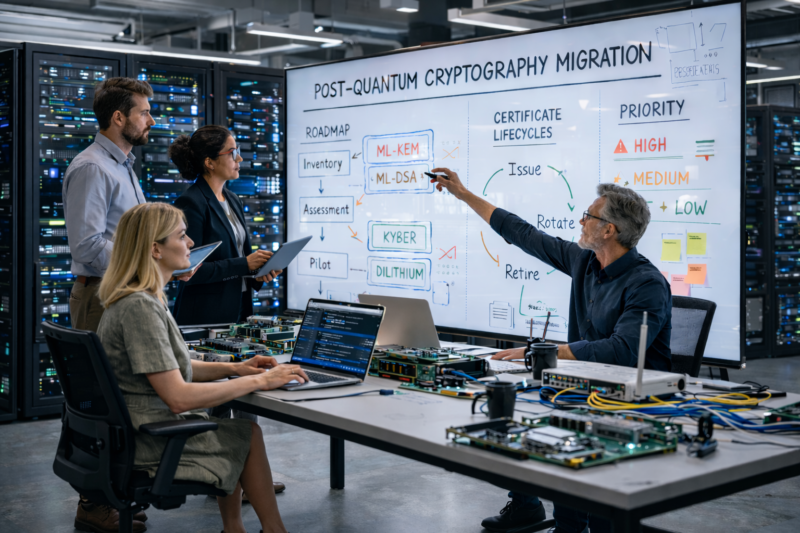
Part 5 – Implementing Quantum-Resistant Encryption
This article moves on to look at executing on your plan – in particular how to choose the appropriate solutions, to implement them effectively, and to future-proof your systems so that they are sustainable.
Part 5 – Implementing Quantum-Resistant Encryption Read More »
Feature series - PQC